The landscape of Android system modification has undergone a seismic shift over the last several years, transitioning from the relatively simple days of bypassing SafetyNet to the complex, multi-tiered requirements of the Play Integrity API. For the enthusiast community, the "Strong Integrity" tier represents the final frontier of device attestation—a hardware-backed security check that ensures a device’s bootloader is locked and its software is untampered. However, with the advent of custom ROMs utilizing unrevoked keyboxes to spoof this attestation, a new technical question has emerged: Does the acquisition of root access jeopardize a device that is already successfully passing the Strong Integrity check?
Recent empirical investigations and cross-device testing have provided a definitive answer to this query, offering a clearer roadmap for users who wish to balance the administrative freedom of root access with the stringent security requirements of modern mobile applications. The consensus among technical analysts suggests that rooting a device running a custom ROM does not inherently cause a failure in Strong Integrity, provided the underlying spoofing mechanism remains undisturbed.
To understand why rooting does not automatically invalidate Strong Integrity, one must first understand the mechanics of the Play Integrity API. Google’s attestation service categorizes devices into three distinct levels of integrity. "Basic Integrity" confirms that the device is a functioning Android unit but may have a compromised bootloader. "Device Integrity" ensures the device meets the profile of a certified Android device. "Strong Integrity," the most demanding tier, requires hardware-backed proof—usually via the device’s Trusted Execution Environment (TEE) or a Secure Element—that the software and hardware haven’t been compromised.
In the custom ROM community, achieving Strong Integrity on a device with an unlocked bootloader was long considered impossible because the hardware itself reports the unlocked state to Google’s servers. The breakthrough came with the discovery of "keybox" spoofing. By injecting an unrevoked cryptographic keybox into the ROM’s framework or kernel, developers can trick the Play Integrity API into believing the device is a different, certified model with a locked bootloader. This override happens at a level deep within the system architecture, often before the operating system fully initializes its security reporting modules.
The primary concern for many users is whether the installation of a root solution—such as Magisk or KernelSU—will interfere with this delicate spoofing setup. To address this, a comprehensive series of tests was conducted across a diverse range of hardware architectures. The testing pool included a wide spectrum of devices: the Poco F5, Nothing Phone 2, OnePlus 11, Samsung Galaxy S20 FE, Galaxy A52s 5G, Redmi 13C, and Moto G54. This selection was intentional, covering various chipsets from Qualcomm, MediaTek, and Exynos, as well as different manufacturer-specific implementations of the Trusted Execution Environment.
The results across all tested units remained consistent: rooting the device had zero negative impact on the Play Integrity status. If a device was passing the Strong Integrity check prior to being rooted, it continued to pass with the same status afterward. This stability is attributed to the fact that root access, in its modern implementation, operates primarily by modifying the boot image or the kernel to allow for superuser permissions. As long as the root solution (like Magisk) is properly hidden from the Play Store and Google Play Services, it does not conflict with the cryptographic "lie" being told by the spoofed keybox.

However, this lack of impact is contingent upon a "clean" root installation. The investigation highlighted a critical distinction: root access itself is benign, but the subsequent actions taken by a user with root privileges are not. The moment a user begins to tinker with system partitions, flash aggressive optimization modules, or alter system properties (build.prop), the risk of failing Play Integrity increases exponentially. Many Magisk modules attempt to modify the device’s fingerprint or system identity to pass Basic or Device integrity. If these modules conflict with the specific identity used by the ROM’s built-in keybox spoofing, the Strong Integrity check will likely fail.
Furthermore, the integrity of the "Strong" status is tied to the validity of the keybox being used. If Google detects that a specific keybox is being used by thousands of unauthorized devices, they can revoke that key server-side. In such an event, the failure of Strong Integrity would be a coincidence of timing rather than a result of the rooting process itself. Users often mistake these server-side revocations for a local failure caused by their most recent system modification.
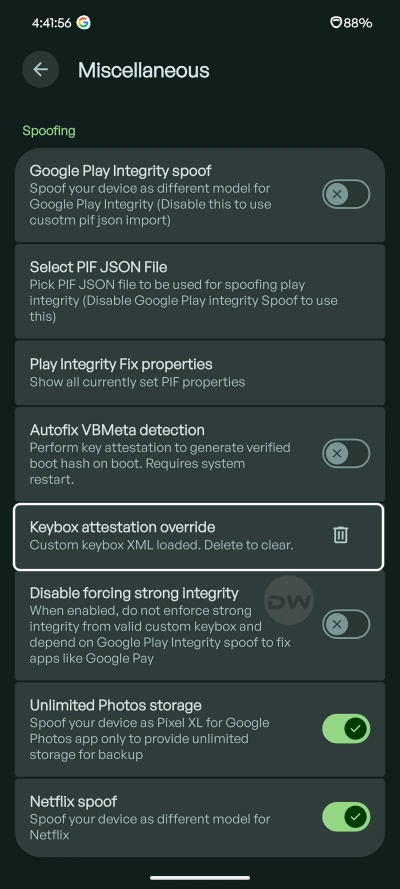
For the rare cases where rooting does appear to disrupt the attestation process, the technical community has developed a suite of remediation tools. If a device fails the Strong Integrity test post-root, the solution usually involves moving away from the ROM’s built-in spoofing and toward a manual, root-managed solution. This involves the use of specific modules such as the Play Integrity Fix (PIF) or the "Tricky Store" module. These tools allow rooted users to manage their own keyboxes and attestation overrides with a higher degree of granularity.
Tricky Store, in particular, has become a vital tool for enthusiasts. It acts as a hardware abstraction layer that intercepts attestation requests and provides the necessary cryptographic signatures using a user-provided keybox. By utilizing such tools, a rooted user can essentially rebuild the Strong Integrity bridge that the ROM had previously provided. This highlights a paradoxical reality in the Android ecosystem: while rooting is technically a violation of the security model Google intends to enforce, it also provides the very tools necessary to simulate compliance with that model.
The broader implication of these findings is significant for the future of Android customization. As banking apps, government services, and high-profile games (such as Pokémon GO or various banking utilities) increasingly move toward requiring Strong Integrity, the ability to maintain root access without losing app functionality is paramount. The current data suggests that the "cat-and-mouse" game between developers and Google has reached a temporary plateau where root and Strong Integrity can coexist, provided the user remains cautious.
In conclusion, the act of rooting a custom ROM that is already passing Strong Integrity is a safe procedure that does not, in isolation, trigger a security flag. The hardware-level spoofing provided by modern ROMs is robust enough to withstand the presence of a superuser binary. Nevertheless, users must remain vigilant. The stability of this environment is fragile, resting on the continued validity of leaked keyboxes and the stealth of root-hiding techniques. While the root itself is not the enemy of Strong Integrity, the misconfiguration of the system following root access certainly can be. For those navigating this complex technical terrain, the rule of thumb remains: root for the power it provides, but exercise restraint in system modification to ensure that the veil of integrity remains intact. As Google continues to refine its attestation algorithms, the community must continue its rigorous testing to ensure that the freedom of the Android platform does not come at the cost of its utility.