The modern Android operating system is often celebrated for its open-source foundations and the perceived autonomy it grants its users; however, a deeper investigation into the core components of the Google Mobile Services (GMS) stack reveals a highly controlled environment where Google exerts significant influence over software versioning. For a subset of power users and developers, the ability to maintain a specific, older version of the Google Play Store is not merely a matter of aesthetic preference but a functional necessity. Whether due to the removal of specific features in newer builds, UI regressions, or compatibility issues with legacy hardware and software, the demand for Play Store downgrading remains high. Yet, the primary obstacle in this endeavor is the Play Store’s aggressive, self-healing architecture, which is designed to automatically update itself in the background, often bypassing standard user-facing settings. This report examines advanced, root-level methodologies for overriding these automated protocols to ensure long-term version persistence.
To understand the complexity of stopping the Play Store from updating, one must first recognize that the application does not behave like a standard third-party utility. In the Android ecosystem, the Play Store is a privileged system entity. While users can navigate to the application’s settings and disable "Auto-update apps," this toggle specifically governs the updates of third-party applications installed via the store; it does not apply to the Play Store binary itself. Google employs hidden background services, frequently referred to as "Self-Update" mechanisms, which monitor the current version of the store and trigger silent downloads and installations of newer builds as soon as a network connection is established. This ensures that the gateway to the Android ecosystem remains secure and compliant with the latest Google policies, but it simultaneously creates a cycle of frustration for users who have intentionally downgraded their software.

For those who find that standard non-root interventions—such as clearing cache or disabling background data—fail to prevent the inevitable update, a more robust approach involving administrative (root) privileges is required. These methods move beyond the surface-level settings and target the underlying service architecture of the Android OS. By utilizing specialized tools such as App Manager and the LSPosed Framework, users can effectively sever the communication lines that the Play Store uses to verify its own version status and fetch updates.
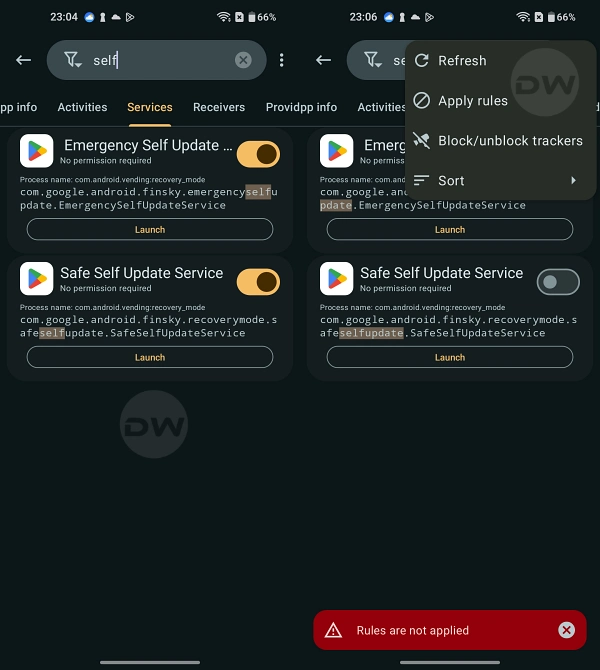
The first sophisticated method involves the use of App Manager, a powerful open-source utility that provides a granular view into the various components of installed applications, including activities, services, and providers that are usually hidden from the user. The logic behind this approach is the surgical deactivation of specific "SelfUpdate" services. Within the internal structure of the Google Play Store (com.android.vending), several services are dedicated to the update lifecycle. These include the "Emergency Self Update Service" and the "Safe Self Update Service." Under normal operating conditions, these services act as watchdogs, checking for the availability of a newer APK on Google’s servers. By leveraging App Manager, a rooted user can intercept these services and apply blocking rules. This process involves searching for the specific "SelfUpdate" strings within the application’s service list and disabling them at the system level. When these components are neutralized, the Play Store loses its ability to initiate the self-update handshake, thereby remaining at the version currently installed on the device.
Alternatively, for users who prefer a framework-based approach, the LSPosed Framework offers a method centered on deception rather than simple deactivation. LSPosed is a modern implementation of the Xposed Framework, allowing users to hook into system processes and modify behavior without altering the physical APK files on the system partition. This is particularly useful for a technique known as "version spoofing." By utilizing a dedicated module, such as PlayVersionSpoofer, users can trick the Android system and Google’s own servers into believing that the device is already running the latest possible version of the Play Store. When the "SelfUpdate" service queries the server, the module intercepts the request and reports a version number that is significantly higher than the one currently available in the public domain. Because the server believes the device is already "ahead" of the update curve, it does not push a new update package. This method is often considered more elegant than service deactivation, as it leaves the application’s internal components intact while effectively neutralizing the update trigger.

However, the implementation of such deep-system modifications is not without inherent risks. The Google Play Store is deeply integrated with Google Play Services (GMS Core), a massive library of APIs that power everything from location services and push notifications to security authentication and in-app billing. When a user forces the Play Store to remain on an older version, they risk creating a version mismatch between the Store and the underlying Play Services. This can lead to unexpected crashes, "Force Close" errors, or the inability to download new applications. Furthermore, because newer versions of the Play Store often include critical security patches and vulnerability mitigations, staying on an older build may expose the device to potential exploits that have been addressed in subsequent releases. Therefore, these procedures are generally reserved for secondary devices or specific testing environments where the need for version control outweighs the requirement for maximum security.
The persistence of these modifications also requires a strategic approach to system maintenance. For instance, if a user decides to revert these changes, they cannot simply uninstall the management tools. Doing so without first removing the applied rules or modules could leave the Play Store in a "broken" state, unable to update even when the user desires it. In the case of the App Manager method, the user must manually navigate back to the service list, locate the "SelfUpdate" components, and remove the blocking rules to restore the "Emergency" and "Safe" update services to their active status. Only after the system’s natural update flow is restored is it safe to remove the utility. Similarly, with the LSPosed method, the spoofing module must be deactivated and the device rebooted to clear the modified hooks from the system memory.
The ongoing battle between user-led version control and Google’s mandatory update policy highlights a broader discourse in the technology industry regarding "ownership" versus "licensing." In the eyes of the developer, the Play Store is a service that must be kept current to ensure the integrity of the ecosystem. In the eyes of the power user, the hardware belongs to the individual, and the software should function according to the individual’s requirements. The methods outlined here—service deactivation via App Manager and version spoofing via LSPosed—represent the current technical frontier for users seeking to reclaim that control.

In conclusion, while Google has made it increasingly difficult to opt-out of the software update cycle, the flexibility of the Android kernel and the ingenuity of the developer community continue to provide pathways for customization. Stopping the Play Store from automatically updating itself is a complex task that requires a transition from standard user interactions to deep system administration. By targeting the specific services responsible for the update mechanism or by spoofing version data through the LSPosed framework, users can achieve a stable, downgraded environment. Nevertheless, such actions necessitate a comprehensive understanding of the Android architecture and a willingness to accept the security trade-offs that come with bypassing the manufacturer’s intended update path. As the Android OS continues to evolve, it is likely that the mechanisms for enforcement and the methods for circumvention will both continue to advance in a perpetual cycle of technical escalation.