A sophisticated cybersecurity threat has infiltrated the Mozilla Firefox extension ecosystem, leading to the immediate removal of several popular browser add-ons that were found to be harboring malicious code. This campaign, identified by security researchers as "GhostPoster," represents a significant escalation in the ongoing battle between browser developers and bad actors who seek to exploit the high-trust relationship between users and their chosen productivity tools. Among the casualties of this purge is the widely utilized "600% Sound Volume" extension, which, along with several others, was discovered to be injecting unauthorized advertisements into the browsing sessions of tens of thousands of users.
The discovery of the GhostPoster campaign has sent shockwaves through the Firefox community, particularly because of the stealthy nature of the infection. According to reports from cybersecurity analysts at Bleeping Computer, the campaign utilizes a highly deceptive method to bypass traditional security screenings: the malicious JavaScript is hidden within the image files of the extensions themselves, such as the application logos. By embedding code within the pixels of an image—a technique known as steganography—the operators behind GhostPoster managed to maintain a persistent presence on more than 50,000 devices. Once an infected extension is installed, the hidden code is extracted and executed, granting the attackers high-privilege access to the browser’s internal functions.
This high-level access is not merely a theoretical risk; it provides the threat actors with a versatile backdoor through which they can conduct a variety of illicit activities. The primary objective appears to be financial gain through various forms of digital fraud. By monitoring browser activity in real-time, the malicious code can identify when a user is visiting an e-commerce platform or a service that utilizes affiliate marketing. The GhostPoster script can then silently hijack the user’s session, replacing legitimate affiliate links with those owned by the attackers. This ensures that any commission generated from the user’s purchase is diverted into the pockets of the cybercriminals rather than the intended marketing partners.
Beyond affiliate theft, the compromised extensions have been found to engage in aggressive ad injection and click fraud. The technical mechanism behind this involves the extension communicating with a remote server, specifically identified as ad.resourcefulman.net. Upon installation, the extension fetches a configuration file—a list of domains stored at a specific subdirectory—which dictates which websites are targeted for ad injection. When a user navigates to a site on this list, the extension attempts to fetch an advertisement banner and injects an iframe directly into the webpage’s Document Object Model (DOM). While some versions of the malware ostensibly ask for user permission before displaying the ad, the underlying infrastructure is designed to bypass standard ad-blocking software and tracking protections, effectively turning the user’s browser into a revenue-generating tool for the GhostPoster operators.
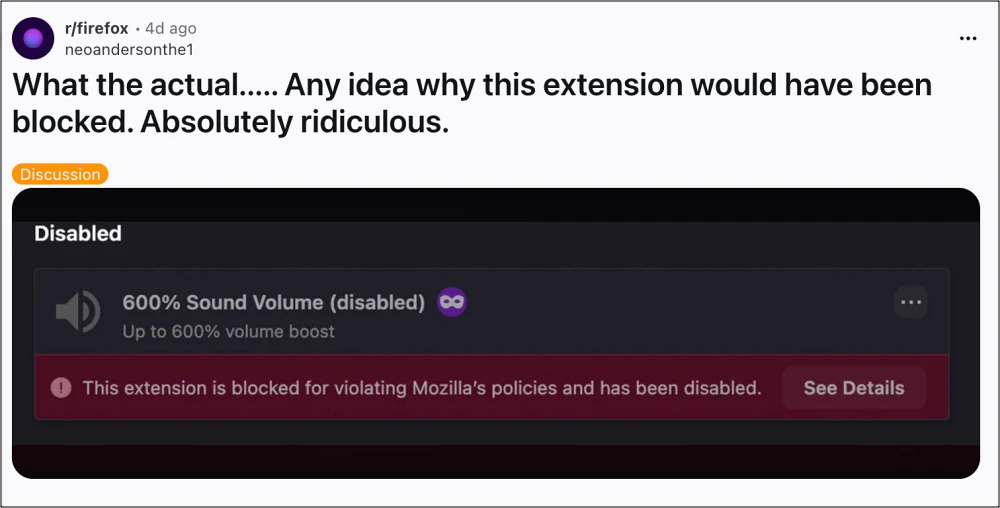
The alarm was first raised by vigilant Firefox users who noticed that "600% Sound Volume," a popular utility for boosting audio output beyond hardware limits, had suddenly vanished from their browser toolbars. Upon checking the Mozilla Add-ons store, users were met with a stark warning stating that the extension had been blocked for violating Mozilla policies and had been remotely disabled on all systems where it was installed. This proactive "kill switch" mechanism is a standard security feature of the Firefox browser, designed to protect users from malicious software even after it has been downloaded. However, the sheer number of affected extensions suggests that the GhostPoster campaign was far-reaching and deeply integrated into the extension marketplace.

While "600% Sound Volume" was the most prominent victim, the list of removed extensions is extensive and includes a wide range of utilities. These range from VPN services like "world-wide-vpn" and "free-vpn-forever" to productivity tools such as "google-translate-pro-extension" and "crxmouse-gesture." Even aesthetic tools were not immune, with "dark-reader-for-ff"—a clone of the legitimate Dark Reader extension—being identified as a carrier for the malicious payload. Other affected add-ons include weather forecasters, MP3 downloaders, and specialized translation tools. The diversity of these extensions indicates that the attackers were not targeting a specific demographic but were instead casting a wide net to capture as many users as possible across different interests and geographic regions.
The use of "backdoor" access is particularly concerning for privacy advocates. Because these extensions require broad permissions to function—such as the ability to "read and change all your data on the websites you visit"—the GhostPoster code can effectively act as a keylogger or a session hijacker. This means that sensitive information, including login credentials, personal communications, and financial details, could potentially be intercepted by the malicious script before it is even encrypted by the website’s HTTPS protocol. The persistent nature of the backdoor allows the operators to update the malicious code remotely, potentially introducing even more dangerous features, such as ransomware or credential harvesting modules, without the user ever being aware of the change.
Mozilla’s response to the threat has been swift, but the incident highlights the inherent vulnerabilities in the browser extension model. Most modern browsers rely on a system of "Manifest" files that define the permissions an extension can request. While Mozilla has implemented rigorous automated and manual review processes, the GhostPoster campaign demonstrates that sophisticated actors can still find ways to hide malicious intent within seemingly innocuous assets like image files. This "supply chain" style of attack is difficult to detect because the extension may behave perfectly for weeks or months before the malicious server triggers the payload, or it may only activate the malicious code for a small percentage of users to avoid detection by security researchers.
For users who may have installed any of the flagged extensions, the recommendation from security experts is clear: immediate removal and a thorough security audit are necessary. While Mozilla has disabled the extensions on many systems, users should manually verify that no remnants of the software remain in their browser settings. Furthermore, because these extensions had the capability to monitor traffic, it is highly advisable for affected users to change their passwords for critical accounts, especially if they logged into those accounts while the extensions were active. Utilizing a reputable password manager and enabling two-factor authentication (2FA) can provide an additional layer of security against the kind of credential theft that high-privilege browser backdoors facilitate.
For those who relied on the functionality provided by the now-removed extensions, several safe alternatives exist. Users of the "600% Sound Volume" add-on are encouraged to look toward established, open-source projects like "SoundFixer" or other privacy-focused volume boosters that have undergone extensive community vetting. The key to maintaining a secure browser environment is to limit the number of installed extensions to only those that are strictly necessary and to favor extensions that are open-source and maintained by reputable developers with a clear history of transparency.
The GhostPoster campaign serves as a stark reminder of the risks associated with the "app store" model of browser customization. While extensions provide invaluable functionality and personalization, they also represent a significant attack surface. As cybercriminals continue to refine their techniques, using steganography and dynamic code fetching to evade detection, the responsibility falls both on browser developers to enhance their vetting processes and on users to remain vigilant. The removal of these malicious extensions is a victory for the security community, but it is likely only one chapter in a much larger story of digital exploitation. As the digital landscape evolves, the "GhostPoster" name will likely remain a cautionary tale of how a simple volume booster can become a silent gateway for global ad fraud and data compromise.