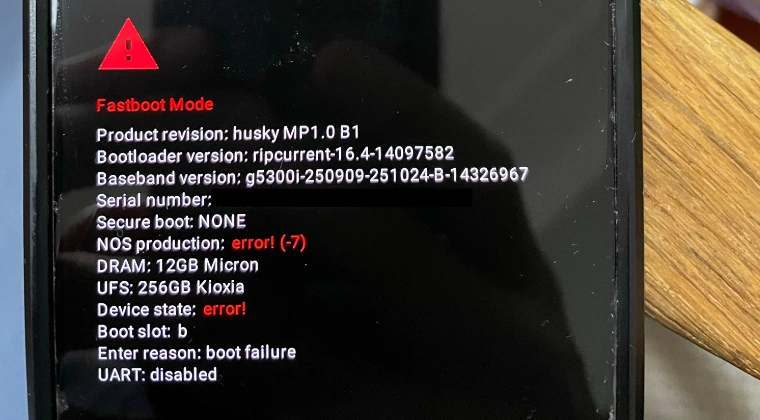
The Google Pixel ecosystem, long celebrated for its seamless integration of high-end hardware and "clean" Android software, is currently facing a significant technical crisis. A growing number of users, particularly those wielding the flagship Pixel 8 Pro, have reported a catastrophic failure in the device’s security architecture. This issue manifests as a total lockout, where the smartphone refuses to recognize valid authentication credentials—such as PINs, patterns, or passwords—and subsequently descends into a non-responsive bootloader state characterized by cryptic error codes. Specifically, the "NOS Production Error (-7)" and "Device State Error (-1)" have emerged as the primary indicators of a deep-seated communication breakdown between the device’s primary processor and its dedicated security hardware.
To understand the gravity of this situation, one must look at the underlying architecture of the modern Pixel device. At the heart of Google’s security promise is the Titan M2, a discrete security chip designed to protect sensitive data, handle secure boot processes, and manage encryption keys. Under normal operating conditions, when a user enters their PIN, the main application processor communicates with the Titan M2 to verify the credentials. If the security chip confirms the data, the device decrypts the user partition and allows access to the operating system. However, the current "NOS Production Error" suggests a failure in the "New Operating System" (NOS) firmware that runs on the Titan chip. When this communication link is severed or corrupted, the device defaults to a state of maximum paranoia, effectively locking the user out of their own data to prevent what it perceives as a potential security breach.
The ordeal typically begins with a subtle but frustrating glitch: the device suddenly rejects a known-good PIN or pattern. Users, assuming a temporary software hiccup, naturally attempt to restart their devices. It is at this juncture that the situation escalates from a minor inconvenience to a critical hardware failure. Instead of booting into the Android environment, the device becomes trapped in Fastboot Mode. In this low-level interface, the smartphone displays the aforementioned error codes: "NOS Production Error (-7)" and "Device State Error (-1)." For the uninitiated, these codes represent a failure of the boot chain to verify the integrity of the hardware state. The device is essentially stuck in a digital "no man’s land," where it cannot proceed to the OS, nor can it access the standard Recovery or Rescue modes.
The phenomenon has caused significant alarm within the Android community, as traditional troubleshooting steps often prove futile. Even a forced shutdown—usually the panacea for mobile glitches—merely results in the device cycling back to the same Fastboot screen. This suggests that the error is not stored in temporary cache but is a persistent state within the Google Security Chip (GSC). While the Pixel 8 Pro appears to be the most affected model, the architectural similarities across the Pixel 6 and 7 series mean that these devices are theoretically vulnerable to similar synchronization failures between the SoC and the secure element.
In response to this escalating issue, several technical workarounds have been identified by the developer community and early adopters. These methods range from simple hardware resets to more complex command-line interventions. While not every method is guaranteed to work for every device, they represent the current frontline of defense against a permanent hardware lockout.
The first and most accessible intervention involves a specific manipulation of the physical hardware buttons. By pressing and holding the Power, Volume Up, and Volume Down buttons simultaneously for approximately thirty seconds, users can trigger a hard reset of the motherboard’s power rail. Unlike a standard restart, this procedure cuts power to the internal components more abruptly, which can sometimes force a recalibration of the communication interface between the CPU and the Titan M2. If successful, the power rail reset clears the "Device State Error" and allows the bootloader to proceed with the standard verification process, eventually leading the user back to the lock screen.
A second, more time-consuming approach involves the total depletion of the device’s battery. This "battery drain" method is based on the principle that even in a stuck Fastboot state, the device is consuming a small amount of power. By allowing the battery to reach zero percent and remain in that state for several hours, any volatile memory within the security chip that might be holding an "error state" flag may eventually clear. Once the device is recharged and powered back on, the "cold boot" sequence might bypass the previous communication error.
For users who are comfortable with the Android Debug Bridge (ADB) and Fastboot environment on a personal computer, there are specific "OEM" commands designed to interface directly with the Google Security Chip. By connecting the Pixel to a PC and utilizing the Fastboot tool, users can attempt to reset the GSC to its factory-default state. The commands "fastboot oem gsc-reset" and "fastboot oem gsc reset-safe" are specifically designed for this purpose. These commands attempt to re-initialize the Titan M2’s internal logic, essentially telling the chip to ignore the previous error state and attempt a fresh handshake with the bootloader. It is important to note, however, that these commands are often restricted on devices with locked bootloaders, which applies to the vast majority of consumer Pixels.
Furthermore, a "hidden" fail-safe mechanism exists within the Pixel’s boot logic. Some users have found success by performing a series of seven consecutive restarts. In certain firmware configurations, the Android system is programmed to recognize a repeated failure to boot as a sign of critical corruption. After the seventh failed attempt, the GSC may trigger an automatic factory reset or force the device into a "Safe Mode" or "Recovery Mode" that was previously inaccessible. While this results in the loss of all local data, it is often preferable to having a completely bricked device.
Despite these potential fixes, there remains a significant cohort of users for whom no software or hardware "tweak" provides relief. In these instances, the "NOS Production Error (-7)" indicates a permanent hardware failure or a level of firmware corruption that cannot be resolved outside of a controlled laboratory environment. When the communication bridge between the processor and the security chip is physically compromised or the Titan M2’s internal firmware becomes non-responsive, the only remaining option is a Return Merchandise Authorization (RMA).
The RMA process is a source of considerable frustration for many, as it involves shipping the device back to Google for repair or replacement. For devices under warranty, this is typically handled at no cost to the consumer, though the loss of data and the downtime without a smartphone remain significant burdens. For those whose devices are out of warranty, the cost of replacing the motherboard—the only way to truly "fix" a failed Titan M2—can be prohibitively expensive. This has led to a broader discussion regarding the "Right to Repair" and the inherent risks of tying a device’s functionality so closely to a single, proprietary security chip that cannot be easily serviced.
As Google continues to investigate the root cause of these errors, the situation serves as a stark reminder of the complexities inherent in modern mobile security. While the Titan M2 provides industry-leading protection against hackers and data thieves, its failure modes are uniquely punishing for the legitimate owner. The "NOS Production Error" is more than just a software bug; it is a symptom of a design philosophy where security takes such a high priority that even a minor synchronization error can render a thousand-dollar device useless. For now, Pixel owners are advised to keep their data backed up to the cloud and to remain vigilant for any signs of authentication instability, as the bridge between a functional phone and a "Device State Error" appears to be thinner than previously imagined.
