The digital landscape has once again shifted with the preliminary rollout of Android 17, the latest operating system iteration from the tech corridors of Silicon Valley. Currently situated in its nascent beta stages, this version primarily serves as a playground for developers and early adopters to test application compatibility and explore the under-the-hood refinements implemented by Google. While the consumer-facing interface remains largely familiar, the architectural changes necessitate a renewed approach to administrative access. Rooting, the process of attaining superuser privileges, remains a cornerstone for power users seeking to transcend the limitations imposed by stock firmware. With the arrival of Android 17, the community has seen a rapid adaptation of tools, offering three distinct methodologies to claim control over the /data and /system partitions: Magisk, APatch, and KernelSU/Next.
The decision to root a device running Android 17 is rarely about cosmetic changes alone; it is an endeavor to reclaim ownership of the hardware. By gaining administrative rights, users can bypass the restrictive sandbox environment that defines modern mobile security. This allows for the integration of sophisticated modifications such as the Fox Magisk Module Manager, which acts as a repository for system-level enhancements. Visual enthusiasts often turn to Substratum Themes to implement system-wide aesthetic changes that go far beyond the native "Material You" capabilities. Furthermore, the installation of the Xposed Framework via the LSPosed bridge remains a vital tool for hooking into system APIs, allowing users to modify the behavior of apps and the OS without touching the underlying source code. For audiophiles, the ability to install Viper4Android remains a primary motivator, providing granular control over audio drivers and digital signal processing that is simply unavailable on unrooted devices.
Beyond software customization, Android 17 rooting facilitates significant hardware optimization. Through the flashing of custom kernels, users can interact directly with the device’s CPU and GPU. This enables the implementation of specific Governor profiles designed to prioritize either extreme battery longevity or peak performance. Advanced users often engage in over-clocking to squeeze additional frames per second out of demanding mobile titles, or under-volting to reduce thermal throttling and extend the lifespan of internal components. These deep-level modifications transform the smartphone from a locked-down appliance into a versatile computing tool.
However, the path to superuser status is fraught with technical caveats and security trade-offs. The prerequisite for any rooting procedure is the unlocking of the device’s bootloader. This action triggers a mandatory factory reset, wiping all user data, and serves as a permanent signal to the manufacturer that the software integrity has been altered. In many jurisdictions, this can nullify the hardware warranty. For users within the Samsung ecosystem, the stakes are even higher due to the Knox security suite. Tripping the Knox fuse is an irreversible hardware-level event; once triggered, secure features such as Samsung Pay, Secure Folder, and certain health tracking metrics become permanently disabled, regardless of whether the user later unroots the device or relocks the bootloader.
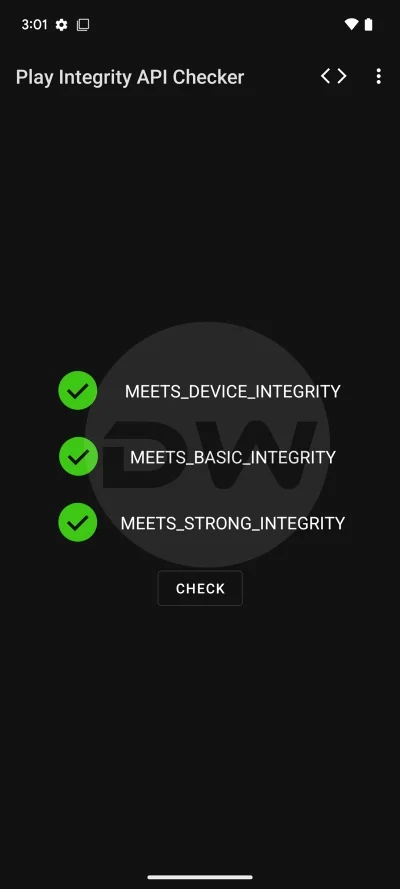
Furthermore, the modern Android security ecosystem relies heavily on the Play Integrity API. Google’s sophisticated attestation mechanism checks whether a device is running a certified, untampered version of the OS. Rooting Android 17 inherently breaks this chain of trust. Consequently, users will find that banking applications, high-security enterprise tools, and popular streaming services like Netflix (which relies on Widevine L1 DRM) may refuse to function or will limit their quality. While the developer community consistently releases fixes to "spoof" integrity checks, it remains a persistent cat-and-mouse game between Google’s security engineers and independent developers.

As we look at the specific methodologies for Android 17, Magisk remains the most recognizable name in the industry. Developed by John Wu, Magisk revolutionized rooting by introducing a "systemless" approach, allowing the system partition to remain untouched while modifications are overlaid via the boot image. For Android 17, the Magisk Alpha branch—an unofficial but highly active development stream—is often the first to provide support for new kernel requirements. Magisk operates by patching the boot image (or the init_boot image in newer devices) with a custom ramdisk. This allows the Magisk daemon to start early in the boot process, granting su access while maintaining the ability to hide the root status from sensitive applications through its "DenyList" feature.
In contrast to the systemless overlay method of Magisk, KernelSU represents a paradigm shift in how administrative access is achieved. Rather than patching the boot image’s ramdisk, KernelSU integrates the root provider directly into the Linux kernel itself. This method is particularly effective for devices running the Generic Kernel Image (GKI) architecture, which Google mandated starting with Android 12. By living inside the kernel, KernelSU is inherently more difficult for user-space applications to detect. It does not require a daemon to manage requests; instead, it uses a kernel-level hook to grant permissions. The "Next" variant of KernelSU further refines this by providing experimental features and support for the latest kernel versions found in the Android 17 beta, making it a preferred choice for those seeking a "stealth" root.
The third and most recent contender in the rooting arena is APatch. This tool seeks to bridge the gap between the modularity of Magisk and the kernel-level integration of KernelSU. APatch functions by patching the kernel, but it does so in a way that allows for the loading of modules similar to Magisk. It utilizes the Loadable Kernel Module (LKM) framework to inject its functionality. One of the standout features of APatch is its ability to provide superuser access without requiring the modification of the system’s init process, which can often be a point of detection for security-conscious apps. For Android 17 users, APatch offers a robust alternative that supports the latest OTA (Over-The-Air) update logic, allowing for a more seamless transition between beta builds.
Executing the root process on Android 17 requires a meticulous setup. The user must first ensure that the Android SDK Platform-Tools are installed on a workstation, as the Fastboot interface is the primary gateway for flashing modified images. The process typically involves downloading the specific factory image or OTA package for the device, extracting the boot.img or init_boot.img, and then utilizing the chosen manager app (Magisk, APatch, or KernelSU) to patch that file. Once the patched image is generated, the device is placed into Bootloader Mode, and the image is flashed via a command-line interface. For devices with A/B partition slots, extra care must be taken to ensure the active slot is targeted correctly to avoid a "bootloop" scenario, where the device fails to initialize the OS.
The evolution of rooting tools for Android 17 demonstrates the resilience of the open-source community. As Google continues to harden the Android kernel and implement stricter hardware-backed attestation, the methods for achieving superuser access have become more sophisticated. Whether through the refined ramdisk patching of Magisk Alpha, the deep kernel integration of KernelSU/Next, or the hybrid LKM approach of APatch, users have more choices than ever. However, these choices come with the responsibility of managing one’s own device security. In an era where mobile devices hold the keys to our financial and personal identities, the decision to break the manufacturer’s security model should be made with a full understanding of the risks involved. For those who proceed, Android 17 offers a powerful, albeit experimental, platform for the next generation of mobile innovation and personalization.