The rise of the "home lab" and self-hosted infrastructure has revolutionized how tech-savvy individuals manage their personal data, moving away from the restrictive silos of Big Tech toward a model of absolute digital sovereignty. By hosting their own media via Plex, managing documents through Nextcloud, and securing credentials in self-hosted password managers, users gain unprecedented control over their privacy and hardware. Yet, this total autonomy introduces a significant, often overlooked vulnerability: the administrator themselves. In the world of high-end home networking and complex server stacks, the individual who builds the system often becomes its single point of failure. If the sole person capable of navigating the command line or decrypting the storage arrays were to become suddenly incapacitated, years of family memories, financial records, and essential smart-home services could be rendered permanently inaccessible. To mitigate this risk, forward-thinking administrators are turning to a concept borrowed from industrial safety and espionage—the Dead Man’s Switch—using specialized open-source tools like Aeterna to ensure their digital legacy survives their own absence.
The concept of a Dead Man’s Switch is rooted in mechanical safety, originally designed to stop a train or machine if the operator became unresponsive. In the digital context, it serves as an automated contingency system that triggers a specific action—usually the distribution of sensitive information—after a predefined period of inactivity. While mainstream providers like Google offer "Inactive Account Managers," these cloud-based solutions are fundamentally ill-equipped for the self-hoster. A Google failsafe can unlock a Gmail account, but it cannot provide the encryption keys for a local ZFS pool or explain the intricate Docker architecture of a home-grown NAS. Furthermore, relying on a third-party corporation to store the "keys to the kingdom" defeats the primary purpose of self-hosting: the elimination of external dependencies. This is why tools like Aeterna have become vital; they allow the administrator to host the failsafe on their own hardware, keeping the most sensitive recovery instructions within their own controlled environment until the exact moment they are needed.

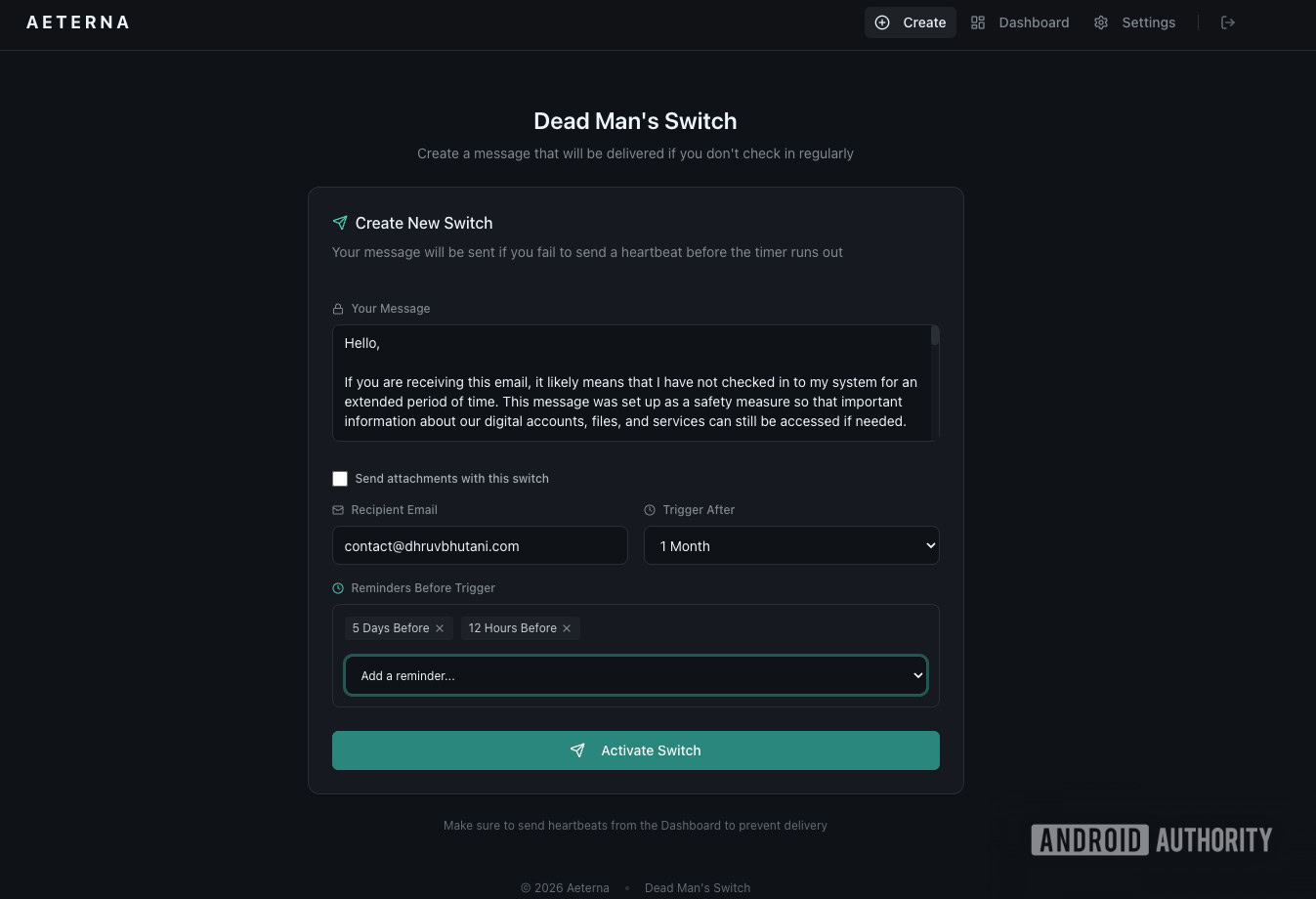
The technical architecture of a self-hosted Dead Man’s Switch is built on a logical framework of three distinct phases: the pulse, the grace period, and the payload. Using Aeterna, a lightweight Docker-based application, an administrator can establish a "pulse"—a recurring check-in that proves they are still active and in control of the system. This can be automated via cron jobs or scripts that ping the server every time a workstation is powered on, but many experienced sysadmins argue for a manual approach. By requiring a deliberate, conscious click on a web interface once a month, the administrator is forced to verify that the failsafe mechanism itself is still operational. This manual interaction serves as a recurring audit, ensuring that the software hasn’t crashed and the underlying hardware remains healthy.
Once a pulse is missed, the system enters the "grace period." This is a crucial buffer zone designed to prevent accidental triggers during vacations, hospital stays, or periods of intense work where server maintenance falls by the wayside. A typical grace period might be set to 30 days, providing a generous window for the administrator to return and reset the timer. Sophisticated setups utilize multi-stage notifications, sending escalating alerts to the administrator at the 15-day and 25-day marks. These warnings act as a final safety net, preventing the system from broadcasting private secrets due to simple forgetfulness. However, if the grace period expires without a pulse, the system assumes the administrator is no longer able to manage the server and proceeds to deploy the "payload."
The payload is the most critical element of the digital legacy plan, acting as a concise, instructional "will" for the family or survivors. Designing a payload requires a delicate balance between technical detail and accessibility. A fifty-page manual on Linux kernel headers is useless to a grieving spouse who just wants to find the family photos; conversely, a simple "good luck" note provides no path forward. A robust payload is typically divided into four essential categories. The first and most vital is access to the primary password manager. Because modern life is increasingly centralized within digital vaults, providing the master password (or instructions on how to find it) is the single most important step in preventing a total lockout of banking, legal, and personal accounts.
The second category involves physical security and two-factor authentication (2FA). In an era of hardware security keys and TOTP codes, a password alone is often insufficient. The payload must guide survivors to the location of physical backup codes or hardware keys, ensuring they don’t get stuck at a secondary login screen. The third category focuses on operational continuity—explaining how to access the photo archives, how to manage the smart home if the lights stop responding, and providing a list of local IP addresses for essential services. Finally, the payload should include a "kill switch" guide. This is a plain-English exit strategy that instructs survivors on how to shut down the complex server rack, which cloud subscriptions to cancel, and how to migrate essential data to a simple, plug-and-play external hard drive.
Security experts, however, raise valid concerns about storing master passwords and 2FA secrets within a software application that might be vulnerable to hackers. To address this, seasoned self-hosters employ a "real-world two-factor" strategy. Rather than placing the actual passwords in the Aeterna payload, the email might instead reveal the location of a physical "In Case of Emergency" envelope hidden within the home. This ensures that even if the server is compromised by a remote attacker, the attacker lacks the physical component required to access the vault. The digital switch tells the survivors where to look, but the physical world keeps the secrets safe until the timer hits zero.
The necessity of such a system highlights the "Bus Factor" in home technology. In software engineering, the Bus Factor represents the number of team members who can be hit by a bus before a project stalls; in most home labs, that factor is exactly one. While enthusiasts spend thousands of dollars on hardware redundancy—RAID arrays to protect against drive failure, Uninterruptible Power Supplies (UPS) to protect against blackouts, and off-site backups to protect against fire—they frequently ignore human redundancy. This creates the "Paradox of Modern Privacy": the more effective an administrator is at securing their data against external threats, the more effectively they accidentally lock out their own family.

The process of setting up a Dead Man’s Switch often serves a secondary, unexpected benefit: it forces a simplification and audit of the entire home lab. If a system is so complex that it cannot be explained in a single, comprehensive email, it is likely too fragile for long-term survival. Writing the payload encourages administrators to clean up legacy DNS settings, document forgotten port-forwarding rules, and streamline their services. It transforms the home server from a chaotic, personal hobby into a documented household asset.
Ultimately, installing a tool like Aeterna is an act of digital responsibility. It acknowledges that while technology can be permanent, its managers are not. By taking the time to configure an automated contingency plan, the self-hoster ensures that their labor—the thousands of hours spent curating libraries, securing records, and building a private digital world—does not become a burden to those they leave behind. A home server should be a legacy, not a locked box in the attic, and the Dead Man’s Switch is the key that ensures the door remains open for the people who matter most.

