The landscape of Android development and beta testing is often characterized by its rapid pace and the immediate availability of resources for developers and enthusiasts. However, the recent rollout of the Android 17 Beta has highlighted a recurring discrepancy in how Google manages its hardware ecosystem, specifically concerning the Pixel 6A. While the majority of the Pixel lineup received simultaneous access to both Over-the-Air (OTA) updates and full factory images, the Pixel 6A was once again conspicuously absent from the official firmware repository. This omission has reignited discussions within the modding community regarding the "cursed" nature of this specific handset, which has historically faced unique software hurdles, including the controversial removal of legacy factory images due to Anti-Rollback (ARB) mechanisms implemented by the tech giant just months prior.

For the average user, the absence of a factory image is a negligible inconvenience, as the OTA update provides a seamless path to the latest software. However, for the community of power users, developers, and those seeking to gain root access, the factory image is an indispensable asset. The primary motivation for obtaining a full firmware package over an OTA file lies in the architecture of the Android boot process. Rooting a modern Android device typically requires the modification of the "boot.img" or the "init_boot.img" file. While these files are technically present within OTA packages, they are often formatted as incremental patches or compressed in a manner that makes them unsuitable for direct extraction and patching. Attempting to utilize a boot image extracted from an OTA file can lead to catastrophic system failures, boot loops, or "soft-bricked" hardware, as these images may lack the full kernel information required for a standalone system boot.
The Pixel 6A’s exclusion from the initial Android 17 Beta factory image list left many users in a state of technical limbo. Google eventually released an OTA image for the device, but the full factory image—the "holy grail" for system modifiers—remained missing. This gap in resource availability forced a pivot toward alternative methodologies for firmware acquisition. The solution emerged from an unlikely source: the official Android Flash Tool. This web-based utility, which utilizes the WebUSB API to allow users to flash firmware directly from a browser, serves as Google’s preferred method for restoring devices. A critical realization among the developer community was that before the tool can flash a device, it must first fetch the full firmware package from Google’s internal servers to the local machine’s temporary storage.

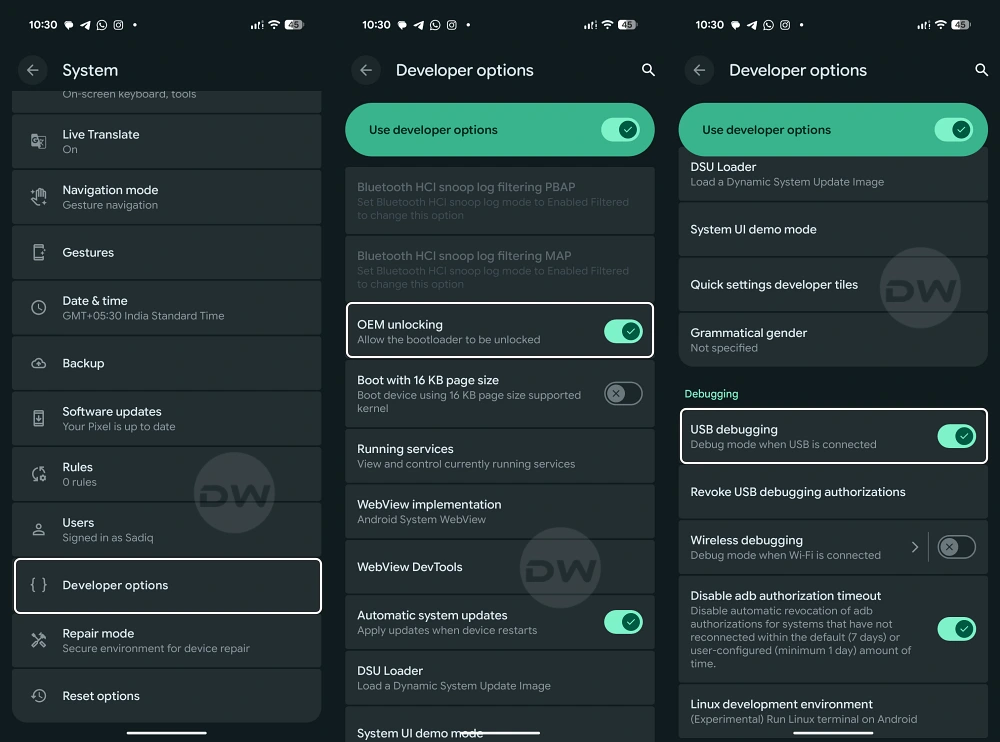
By leveraging this operational sequence, it is possible to intercept the direct download URL for the firmware before the flashing process concludes. This discovery provides a reliable workaround for obtaining full factory images even when they are not listed on the public-facing Google Developers portal. The process involves initiating a standard session with the Android Flash Tool, selecting the desired build for the connected device, and monitoring the network traffic via browser developer tools. Within the network log, a high-volume data request typically points toward a Google-hosted URL containing the complete ZIP archive of the firmware. This captured link allows the user to download the full image independently, providing them with the necessary files to proceed with advanced system modifications without relying on the public repository.
The technical validity of this method was recently confirmed through successful real-world application. Upon capturing the hidden URL and downloading the full package, enthusiasts were able to verify the integrity of the firmware. Unlike fragmented OTA updates, this package contained the comprehensive suite of system partitions. Once the firmware was downloaded, the extraction of the "image-bluejay.zip" (the specific codename for the Pixel 6A) revealed the elusive "boot.img." This file was then processed through Magisk to create a patched version, which was subsequently flashed via the Fastboot interface. The result was a successful root of the Android 17 Beta on a device that, by all official accounts, did not yet have the public resources available to support such a procedure.

This breakthrough is significant not just for Pixel 6A owners, but for the broader philosophy of device ownership and software transparency. It demonstrates that the infrastructure Google has built to simplify device recovery can also be repurposed by the community to ensure that "cursed" devices are not left behind in the development cycle. However, this methodology is not without its complexities. The primary requirement for this "interception" method is that the user must be prepared to allow the tool to begin the flashing process, which traditionally involves a complete data wipe of the handset. While there are theoretical methods to circumvent the data wipe—such as disconnecting the device or manipulating the flashing script—these actions introduce a high degree of risk.
The risks associated with manual firmware manipulation on beta software cannot be overstated. Beta versions of Android, particularly early releases like Android 17, are inherently unstable. When combined with the complexities of Anti-Rollback protections, which prevent users from downgrading to more stable versions of the OS, the margin for error is razor-thin. If a user flashes an incorrectly patched boot image or interrupts a flash at a critical juncture, the device may enter a state that requires professional recovery. This is why the community emphasizes the necessity of comprehensive data backups before attempting any procedure involving the Android Flash Tool or manual Fastboot commands. The digital "safety net" provided by Google is robust, but it is designed for standard use cases, not for the granular manipulation required for rooting and custom development.

Furthermore, the history of the Pixel 6A suggests that Google may have specific internal reasons for delaying or restricting its factory images. The previous removal of Android 15 and older images was a drastic measure intended to prevent users from rolling back to versions with known security vulnerabilities that could be exploited to bypass hardware-level protections. This "wrath of Google," as some enthusiasts call it, is often a byproduct of stringent security engineering. By finding a way to extract the firmware through the Flash Tool, users are essentially finding a back door into a room that Google has temporarily locked for maintenance.
As the Android ecosystem continues to evolve, the tools available to the community must evolve in tandem. The shift toward web-based flashing utilities like the Android Flash Tool represents a move toward greater accessibility, but it also centralizes control over how and when firmware is distributed. The ability to "sniff" network traffic to retrieve direct links is a vital skill for the modern power user. It ensures that the community remains independent of the arbitrary delays that often plague specific device models.

In conclusion, the journey to rooting the Android 17 Beta on the Pixel 6A serves as a masterclass in technical persistence. It highlights the importance of understanding the underlying mechanics of official tools and the differences between various firmware distribution formats. While Google may occasionally falter in providing a consistent experience across all devices in its portfolio, the ingenuity of the user base ensures that there is almost always a path forward. This method of firmware extraction is now a documented strategy in the developer’s toolkit, providing a reliable fallback for whenever a device finds itself excluded from the official factory image repository. As always, those who choose to walk this path do so at their own risk, armed with the knowledge that in the world of Android, the "impossible" is usually just a hidden URL away.